Hidden fields. Top charts.
- Send and read messages | Slack.
- Share this story.
- The Best Encrypted, Secure Messaging Apps;
- What is the Way to Monitor Things With Your Phone.
- Messages, files, channels and people: your four search categories.
New releases. Add to Wishlist.
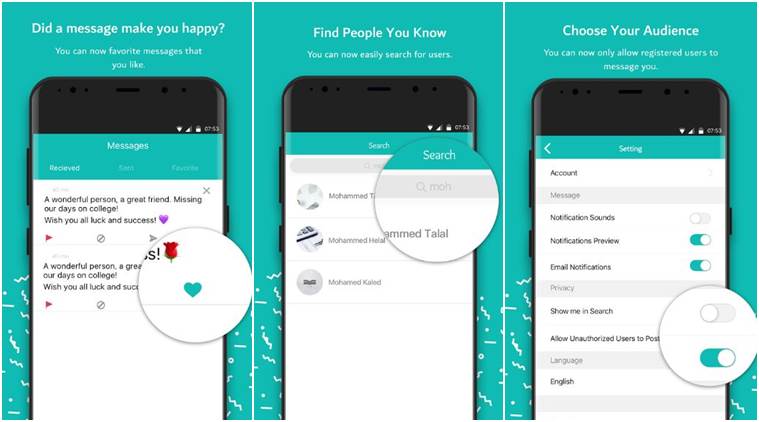
Message anyone from anywhere with the reliability of texting and the richness of chat. Stay in touch with friends and family, send group texts, and share your favorite pictures, GIFs, emoji, stickers, videos and audio messages. Chat features RCS On supported carriers, you can send and receive messages over Wi-Fi or your data network, see when friends are typing or when they have read your message, share images and videos in high quality, and more.
Others separate attachments from messages and save them in a specific directory.
Though its use is not strictly defined, URLs of this form are intended to be used to open the new message window of the user's mail client when the URL is activated, with the address as defined by the URL in the To: field. Many email providers have a web-based email client e. This allows users to log into the email account by using any compatible web browser to send and receive their email. Mail is typically not downloaded to the web client, so can't be read without a current Internet connection.
The Post Office Protocol 3 POP3 is a mail access protocol used by a client application to read messages from the mail server. Received messages are often deleted from the server. Small portable devices like smartphones are increasingly used to check email while traveling and to make brief replies, larger devices with better keyboard access being used to reply at greater length. IMAP shows the headers of messages, the sender and the subject and the device needs to request to download specific messages.
Usually, the mail is left in folders in the mail server. Email has been widely accepted by businesses, governments and non-governmental organizations in the developed world, and it is one of the key parts of an 'e-revolution' in workplace communication with the other key plank being widespread adoption of highspeed Internet. Email marketing via " opt-in " is often successfully used to send special sales offerings and new product information. Many users access their personal emails from friends and family members using a personal computer in their house or apartment.
What We Considered
Email has become used on smartphones and on all types of computers. Mobile "apps" for email increase accessibility to the medium for users who are out of their homes. While in the earliest years of email, users could only access email on desktop computers, in the s, it is possible for users to check their email when they are away from home, whether they are across town or across the world.
Alerts can also be sent to the smartphone or other devices to notify them immediately of new messages. This has given email the ability to be used for more frequent communication between users and allowed them to check their email and write messages throughout the day.
Shrinking the haystack: how to narrow search results in Slack
As of [update] , there were approximately 1. Individuals often check emails on smartphones for both personal and work-related messages. It was found that US adults check their email more than they browse the web or check their Facebook accounts, making email the most popular activity for users to do on their smartphones. However, the percentage of consumers using email on a smartphone ranges and differs dramatically across different countries. As of [update] , the number of Americans visiting email web sites had fallen 6 percent after peaking in November For persons 12 to 17, the number was down 18 percent.
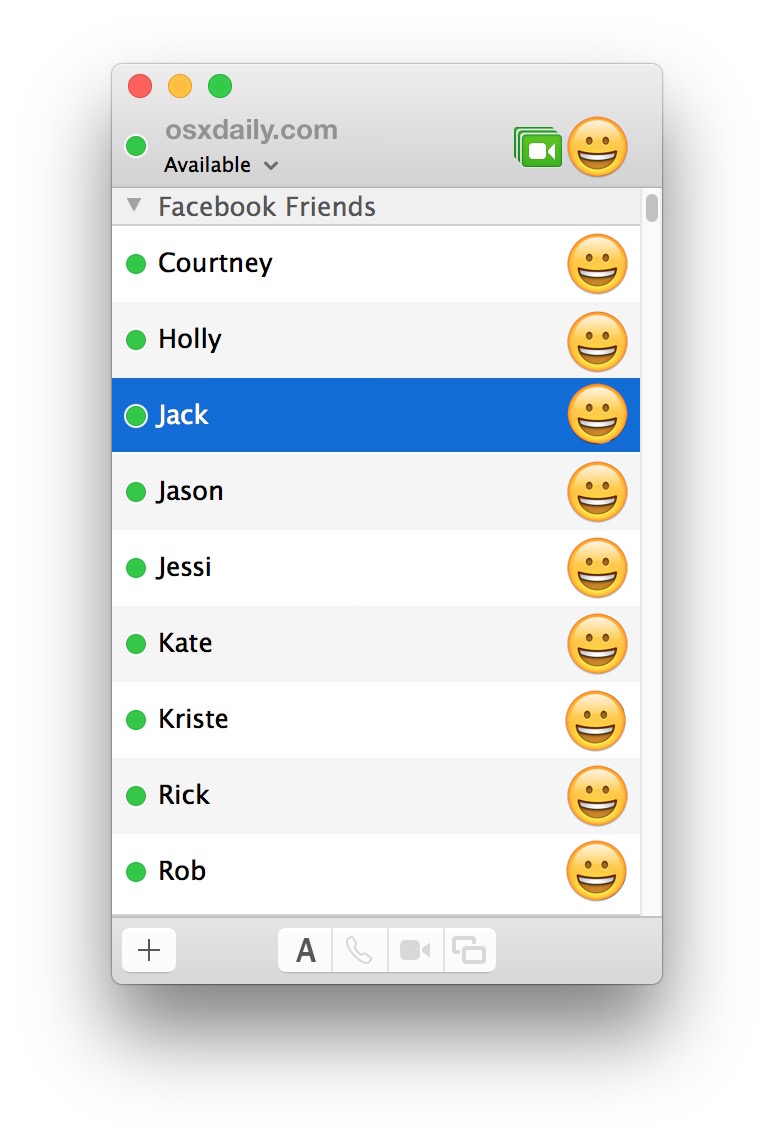
Young people preferred instant messaging , texting and social media. A survey of Android users showed that persons 13 to 24 used messaging apps 3. Email messages may have one or more attachments, which are additional files that are appended to the email. Typical attachments include Microsoft Word documents, PDF documents, and scanned images of paper documents. In principle, there is no technical restriction on the size or number of attachments. However, in practice, email clients, servers , and Internet service providers implement various limitations on the size of files, or complete email - typically to 25MB or less.
WhatsApp general tips and tricks
Where larger files need to be shared, various file hosting services are available and commonly used. The ubiquity of email for knowledge workers and "white collar" employees has led to concerns that recipients face an " information overload " in dealing with increasing volumes of email. This can lead to increased stress and decreased satisfaction with work.
Some observers even argue it could have a significant negative economic effect, [80] as efforts to read the many emails could reduce productivity. Email "spam" is unsolicited bulk email. The US CAN-SPAM Act of and similar laws elsewhere [84] had some impact, and a number of effective anti-spam techniques now largely mitigate the impact of spam by filtering or rejecting it for most users, [85] but the volume sent is still very high—and increasingly consists not of advertisements for products, but malicious content or links.
A range of malicious email types exist. These range from various types of email scams , including "social engineering" scams such as advance-fee scam "Nigerian letters", to phishing , email bombardment and email worms. Email spoofing occurs when the email message header is designed to make the message appear to come from a known or trusted source. Email spam and phishing methods typically use spoofing to mislead the recipient about the true message origin. Email spoofing may be done as a prank, or as part of a criminal effort to defraud an individual or organization.
An example of a potentially fraudulent email spoofing is if an individual creates an email that appears to be an invoice from a major company, and then sends it to one or more recipients. In some cases, these fraudulent emails incorporate the logo of the purported organization and even the email address may appear legitimate. Email bombing is the intentional sending of large volumes of messages to a target address. The overloading of the target email address can render it unusable and can even cause the mail server to crash. Today it can be important to distinguish between the Internet and internal email systems.
Internet email may travel and be stored on networks and computers without the sender's or the recipient's control. During the transit time it is possible that third parties read or even modify the content. Internal mail systems, in which the information never leaves the organizational network, may be more secure, although information technology personnel and others whose function may involve monitoring or managing may be accessing the email of other employees.
There are cryptography applications that can serve as a remedy to one or more of the above. Additionally, many mail user agents do not protect logins and passwords, making them easy to intercept by an attacker. Encrypted authentication schemes such as SASL prevent this. Finally, the attached files share many of the same hazards as those found in peer-to-peer filesharing.
Attached files may contain trojans or viruses. Emails can now often be considered as binding contracts as well, so users must be careful about what they send through email correspondence.
Set and manage disappearing messages – Signal Support
Flaming occurs when a person sends a message or many messages with angry or antagonistic content. The term is derived from the use of the word incendiary to describe particularly heated email discussions. The ease and impersonality of email communications mean that the social norms that encourage civility in person or via telephone do not exist and civility may be forgotten. Also known as "email fatigue", email bankruptcy is when a user ignores a large number of email messages after falling behind in reading and answering them.
The reason for falling behind is often due to information overload and a general sense there is so much information that it is not possible to read it all. As a solution, people occasionally send a "boilerplate" message explaining that their email inbox is full, and that they are in the process of clearing out all the messages. Harvard University law professor Lawrence Lessig is credited with coining this term, but he may only have popularized it.
MIME now allows body content text and some header content text in international character sets, but other headers and email addresses using UTF-8, while standardized [94] have yet to be widely adopted. The original SMTP mail service provides limited mechanisms for tracking a transmitted message, and none for verifying that it has been delivered or read.